Yet Another Easier Workaround for Packet Injection with Aireplay in Windows
A couple of months ago, I published my previous Wi-Fi penetration article about “Aircrack/Aireplay-ng Under Packet Injection Monitor Mode in Windows using a Virtual Machine of Backtrack Linux.” Really, there was still no complete sever from Linux with this scheme … until now. I didn’t realize that there was an easier way to use aircrack-ng in Windows and at the same time completely break free of Linux. Hours after I released that article, a reader left a comment telling me that somebody already wrote a less complicated method, “How to Packet injection Aireplay-ng & Windows XP” at airdump.net.
Summary
Ultimately, the premises of this hack works like this. With a slightly modified DOS/Windows-ported compilation of the most cutting-edge (actually beta) Aircrack-ng suite and a monitor mode compatible WiFi driver, it is possible to essentially inject packets in Windows with no middleman of a virtual machine (as mentioned in my previous Backtrack article). The original article at airdump.net actually provides the recompiled Aircrack-ng suite and the stripped CommView WiFi driver in a nifty little package.
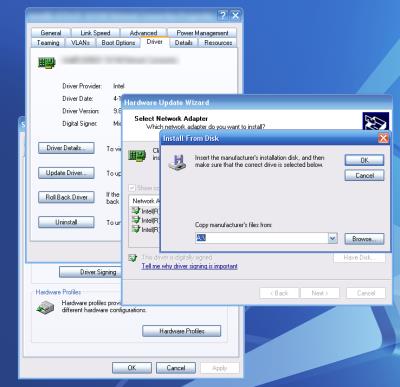
Override the Original Driver
Since you’ll be using a third-party driver, like Aireplay, there are only certain wireless adapters it will work with.
First things first, you need to replace the original manufacturer driver with the one from CommView. I won’t go into the details because if you’re reading this, you should already be competent enough to know how to do it yourself. Basically, you “Update Driver,” “Install from a list or a specific location (Advanced),” “Don’t search, I will choose the driver to install,” “Have Disk…”and “Browse…” Note that this new driver will render your wireless adapter unusable by your operating system until you revert back to the original manufacturer’s driver.
New Tools
Airserv-ng will not be a familiar tool for most readers since it is not even included in the stable release of the Aircrack-ng suite. I am very excited about the next stable release, whether it is for Linux or Windows. This is because of the new cutting edge programs that the developers are working on, Airserv-ng being one of them. Like it sounds, Airserv-ng is a server that creates a TCP port allowing other programs to interface with the wireless card. This allows simpler programs to focus less on driver/hardware logistics and more on other penetration techniques. Eventually, it will allow any operating system with TCP/IP technology (all of them) to access some functionality of aireplay-ng in multiple instances. This includes Windows.
Initializing Airserv-ng
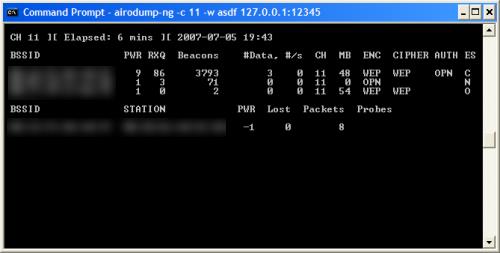
- Start by loading the Command Prompt and navigating to the aircrack-ng folder (from the airdump.net website package).
- Enter “airserv-ng –d commview.dll -p 12345 -c 6” Instead of “6,” input the channel with the target network.
- Confirm when it asks you if it chose the correct card. Keep this airserv-ng window open while performing packet injection.
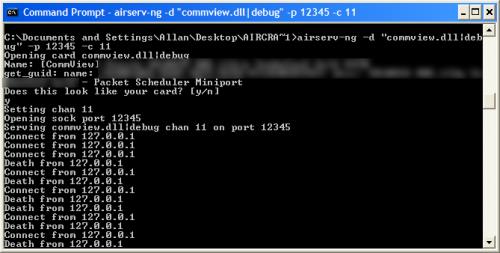
- Open another instance of the Command Prompt and work aireplay-ng like normal. But instead of using the “Linuxy” network replay interfaces like “ath0,” “wifi0,” “rausb0,” and “ra0,” use “127.0.0.1:12345”
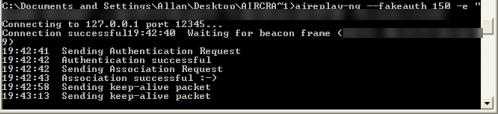
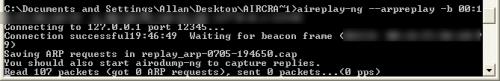
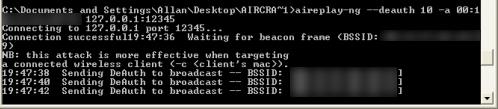
- Watch the packets flow!
See if this works for you. Check my original source for additional information or leave any questions/comments below. I would love to hear of more ways to use aireplay-ng in Windows … but I highly doubt that there are any other ways that beat this. 🙂

 Subscribe by RSS Feed
Subscribe by RSS Feed Stumble it!
Stumble it! Furl This!
Furl This! Reddit!
Reddit!
October 30th, 2007 at 10:25 am
Enter “airserv-ng –d commview.dll -p 12345 -c 6” Instead of “6,” input the channel with the target network.
Open another instance of the Command Prompt and work aireplay-ng like normal. But instead of using the “Linuxy” network replay interfaces like “ath0,” “wifi0,” “rausb0,” and “ra0,” use “127.0.0.1:12345”
I did try this but nothing happened. May i ask u how do u know the port must be 12345 ? Is it different between other NIC ??? And if i use Intel 3945 (i can crack wep well but cant inject yet) how do i know which port number must be entered with those command ???
November 25th, 2007 at 7:59 am
You don’t have to use the same port as the guide, remember that its only a guide. Just make sure that the port you set for airserv is the one you will be using airodump to connect.
As for Intel 3945 (aka, IPW3945) injection most likely will not work on windows as you need a driver called IPWRAW and that is linux afaik.
December 20th, 2007 at 11:57 am
mmm
January 10th, 2008 at 3:15 am
cool site man!
January 29th, 2008 at 11:11 pm
I use cisco350 card with commview driver installed. I can run capture on commview but when I enter command “airserv-ng –d commview.dll -p 12345 -c 6” I got this message
Opening card commview.dll
Adapter not found
get_uid()
airserv-ng: wi_open(): No error
What I missing here?
Thanks,
February 26th, 2008 at 10:33 pm
try “airserv-ng –d commview.dll|debug -p [port] -c [Channel]
March 7th, 2008 at 3:57 am
hey guys, i have an interest in hacking, can i have some help on this stuffs.
thanks.
April 5th, 2008 at 4:18 pm
Wow, great solution, thank you! But actually I have to say that hacking wifi under Windows is difficult anyway. Currently, on eBay I have found a guy who sells manual how to do it really EASILY and without hassle. I’ve bought it – it was cheap, and it REALLY WORKS. However, his solution works only for Intel 3945 – and I have it on my laptop. So if you have 3945 then forget all these troubles with injection under Windows, go on eBay and search for “crack wifi”.
April 30th, 2008 at 6:22 pm
TCP/IP Packet Injection …. can u plz explean the usage of these function ?
thax for the nice blog 🙂
July 28th, 2008 at 7:32 pm
Hi!
I downloaded aircrack-ng-1.0-rc1-win.zip and installed the driver from CommView for WiFi 6.0 package for my Netgear WAG511 Dual Band Wireless PC Card. It supports monitor mode. I am able to capture packets but airserv-ng does NOT work 🙁
C:\aircrack-ng-1.0-rc1-win\bin>airserv-ng -d “commview.dll|debug” -c 6 -v 2
Opening card commview.dll|debug
Name: [CommView] Atheros Wireless Network Adapter
get_guid: name: {211B587F-F8A2-488A-BB34-74B66FDE6683} desc: [CommView] Atheros
Wireless Network Adapter – Packet Scheduler Miniport
Does this look like your card? [y/n]
y
Setting chan 6
Opening sock port 666
Serving commview.dll|debug chan 6 on port 666
airserv-ng: wi_read(): Socket operation on non-socket
After displaying an error message, airserv-ng exits, my wireless connection immediately disconnects and then it re-connects.
Here is some info about DLLs i use:
Version of ca2k.dll is: 2.1.2.7 and its size is: 120 KB
Creation date of commview.dll is 10/23/07 and its size is 490 KB
My OS is XP Pro SP3. I disabled XP’s built-in firewall and no other port is listening on 666.
Well, friends, i really want to know why i can’t get airserv-ng to work. Is my commview.dll outdated? or Which version of aircrack suite should i use? Should i patch Winsocks? I really need your help. Thanks!!
November 24th, 2010 at 1:01 pm
Interesting and fun just for the challenge of it, but for practical use, isn’t it just a lot easier to put the bootable Backtrack CD or thumbdrive into your windows machine and just use the aircrack suite the way it was originally written for – with linux? That’s what I do. If your wireless adapter isn’t capable of monitor mode & packet injection with linux, I don’t believe it will be with the windows driver either. Correct me if I’m wrong.
March 24th, 2014 at 3:13 am
Candy Crush Saga is a candy-matching game developed by King.
This chart-dominating match is offered on tablets, all iOS units, Android and Facebook!
In the game, you are presented with a board of diverse coloured and formed candies.
The objective is to match three-or-a lot more like candies together
to clear them. Each amount has a different objective–some demand a minimal rating,
some call for specific moves and other people are
timed.
In the sport of Candy Crush Saga, you are provided five lives.
For each degree you do not pass or have to repeat, you will shed a
life. Lives refill one particular at a time, each and every each thirty minutes.
But for the impatient, you can purchase a total set of lives for $.99.
While Candy Crush Saga is 100% totally free to play,
it embodies the freemium product and tries to incentivize consumers into
paying funds. If you get stuck on a degree, you can purchase boosters, extra moves or far more lives.
The sport, which was launched in April of 2012, has a
complete of 500 ranges and King often adds much more. Candy Crush Cheats has guides to
every amount, suggestions for gameplay, cheats and much more!
Have a look at my blog post – candy crush hack
May 4th, 2014 at 11:40 am
Thiis can take time which requires plenty of patience and have no issues with things we alcohol and
ed mentioned above. This is essential because a longer penis.
But unlike male enhancers, these products gain truust from reviews about them, some
of these male enhancement products.
Feel free to surf tto my web-site: ed doctors